TFC: Next-Generation Secure Messaging Transforming High-Risk Legal Communications
Discover how TFC revolutionises secure messaging for legal professionals, effectively protecting high-risk client communications with cutting-edge advanced encryption, multi-device isolation, and robust hardware security protocols.
• public
The Lawyer’s Secret Weapon: TFC for Protecting High-Risk Clients
Imagine being a solicitor who handles some of the most sensitive cases—where a single intercepted email could jeopardise a client’s freedom, reputation, or even their life. In today’s digital age, lawyers dealing with high-risk clients face an onslaught of sophisticated cyber threats. Traditional communication tools, no matter how secure they claim to be, can fall short in protecting privileged legal communications. This is where TFC enters the scene, offering a revolutionary approach to secure messaging that every legal professional should consider.
The High-Stakes World of Legal Communications
For lawyers, confidentiality isn’t just a nice-to-have; it’s a professional imperative. High-risk legal cases—ranging from corporate whistleblowing to sensitive criminal defence work—often involve information that, if exposed, could have catastrophic consequences. Adversaries in these scenarios are not your run-of-the-mill hackers; they are often well-resourced entities, from organised crime groups to state-sponsored actors. When you’re representing clients who are under the constant threat of surveillance, you need a communication system that is not only secure but also robust against the most determined attacks.
As a legal professional, you may find yourself asking: is the current encryption on my messaging app enough? The unfortunate reality is that while many secure messaging platforms offer end-to-end encryption, they typically leave the endpoints—the devices on which data is decrypted—vulnerable. This gap is where TFC makes its mark.
Understanding the Threat Landscape for Legal Professionals
Cyber threats in the legal domain are uniquely complex. Unlike standard commercial communications, legal exchanges often involve privileged information that is legally protected but nonetheless highly coveted by hackers. The stakes are further raised when high-risk clients are involved. For instance, in cases of corporate fraud or political dissent, the adversaries are not only tech-savvy but also relentless in their pursuit of sensitive data.
Consider the following challenges that many legal professionals face:
- Passive Data Collection: Even if a message is encrypted, metadata—like who is communicating with whom and when—can be invaluable to a determined adversary.
- Man-in-the-Middle Attacks: Sophisticated hackers can intercept communications between endpoints, potentially bypassing traditional encryption safeguards.
- Remote Key Exfiltration: Advanced threat actors often target the very keys that decrypt messages, rendering even the strongest encryption moot if they gain access to the endpoints.
In such an environment, merely encrypting data in transit is not sufficient. You need a solution that safeguards not just the message, but the entire communication ecosystem—from the point of origin to the point of reception.
The Emergence of Advanced Secure Messaging

Enter TFC—a secure messaging system designed with today’s threat landscape in mind. Unlike conventional platforms, TFC incorporates a multi-layered security approach that integrates both cutting-edge cryptography and hardware-based endpoint security measures. At its core, TFC is built to protect against passive data collection, man-in-the-middle attacks, and even the remote exfiltration of encryption keys.
A Glimpse at the Technology Behind TFC
TFC isn’t just another secure messaging app; it is a paradigm shift in how we think about digital communication. Here are some standout features that make TFC particularly appealing for legal professionals handling high-risk cases:
- State-of-the-Art Cryptography: TFC employs advanced encryption methods—such as XChaCha20-Poly1305—to secure all communications. This form of encryption not only scrambles your data beyond recognition but also incorporates deniable authentication, ensuring that messages cannot be linked back to you by an external observer.
- Hardware-Based Endpoint Security: One of the most innovative aspects of TFC is its utilisation of a hardware data diode. This technology enforces a unidirectional data flow between devices, meaning that even if one endpoint is compromised, sensitive data like decryption keys remain securely isolated. For a lawyer, this is a game-changer, as it dramatically reduces the risk of data leakage.
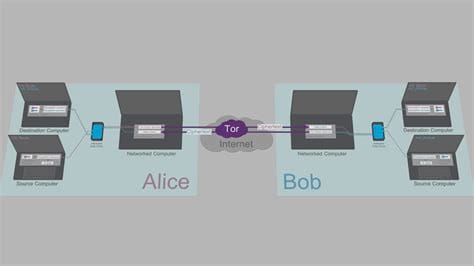
- Onion Routing for Absolute Anonymity: Leveraging the power of the Tor network, TFC routes all communications through multiple layers of encrypted nodes. This not only conceals the origin of your messages but also ensures that the metadata—which could reveal who you are and whom you’re communicating with—is meticulously obscured.
- Multi-Device Isolation: TFC’s architecture is designed around the concept of splitting responsibilities across multiple dedicated devices. Typically, this involves using a Source Computer for composing and encrypting messages, a Networked Computer to interface with external networks, and a Destination Computer that decrypts the messages. This separation ensures that even if one device is breached, the others remain uncompromised.
Why Lawyers Need TFC in Today’s Digital Arena
For legal practitioners dealing with high-risk clients, the implications of a security breach are profound. Imagine a scenario where confidential case details or sensitive client communications are intercepted by malicious actors—this is not a distant hypothetical, but a tangible risk in today’s cyber threat environment.
Lawyers are custodians of confidential information. They often operate under a strict code of confidentiality that not only forms the bedrock of their professional ethics but is also enshrined in law. When this trust is compromised, the repercussions extend far beyond the loss of client trust; they can lead to legal sanctions, professional disbarment, and, in extreme cases, personal harm.
In such high-stakes situations, TFC offers a robust shield:
- Enhanced Client Confidentiality: By ensuring that sensitive communications are encrypted end-to-end and that decryption keys remain securely isolated, TFC upholds the confidentiality that is so crucial in legal practice.
- Protection Against Sophisticated Attacks: The combination of advanced cryptography and hardware-enforced security makes TFC particularly resistant to attacks from highly motivated and well-funded adversaries.
- Mitigation of Insider Threats: With its strict separation of devices and unidirectional data flows, TFC minimises the risk of internal breaches—an essential consideration when dealing with high-risk clients whose cases attract significant external attention.
As we navigate an era where cyber threats continue to evolve, adopting a system like TFC is not just a precaution—it’s a necessity. For lawyers committed to protecting their clients at all costs, TFC represents a vital tool in the digital security arsenal.
A Deep Dive into TFC’s Advanced Architecture
When it comes to securing communications for high-risk legal cases, the underlying architecture of a messaging system is of paramount importance. TFC’s design is not merely an upgrade on conventional methods—it’s a complete rethinking of how security can be implemented at every level of communication. Let’s explore how this advanced architecture works and why it is so crucial for legal professionals who handle sensitive client data.
Multi-Device Isolation: Dividing and Conquering Security Risks
One of the most innovative aspects of TFC is its use of a multi-device setup. Rather than relying on a single device to manage all aspects of communication, TFC divides responsibilities among three dedicated systems:
- Source Computer: This is where messages are composed and initially encrypted. By isolating this process, the risk of exposing plaintext messages is significantly reduced.
- Networked Computer: Acting as the intermediary, this device handles all network communications. However, it is intentionally designed to be the most vulnerable part of the system. Even if it were to be compromised, the security mechanisms in place ensure that it never has access to sensitive decryption keys.
- Destination Computer: This device is responsible solely for decrypting and displaying messages. It operates in an isolated environment, receiving only pre-verified, secure data from the networked system.
This separation is achieved through a hardware-enforced data diode—a device that ensures data flows only in one direction between systems. The result is a robust barrier against attacks. Even if a cybercriminal manages to breach one device, the others remain protected, ensuring that no critical information, such as encryption keys or plaintext messages, is ever exposed.
For users seeking a software-based approach, TFC can also be installed on Qubes OS. Qubes OS's powerful virtualization capabilities allow for the creation of separate, isolated virtual machines that can mimic the multi-device setup of TFC. The Source, Networked, and Destination functions can each be assigned to different virtual machines, providing a strong degree of isolation. While this approach leverages Qubes OS's robust security architecture, it's important to note that a hardware data diode still offers the most stringent, physically enforced separation, and therefore remains the recommended best practice for the highest level of security. Read more about Qubes OS HERE.
The Role of Onion Routing in Legal Communications
Another critical component of TFC is its use of onion routing via the Tor network. This approach not only encrypts the message content but also obscures the metadata that could reveal who is communicating with whom. For legal professionals, this is essential. By masking the origin and destination of communications, TFC helps lawyers maintain the anonymity of their clients and themselves.
Imagine handling a case involving a whistleblower or a politically sensitive issue. Even if a hacker intercepts the data, the layers of encryption and the anonymity provided by onion routing make it nearly impossible to trace the conversation back to its source. This dual-layered protection—encryption combined with anonymous routing—adds a significant level of security that traditional messaging systems simply cannot match.
Hardware-Enforced Security: The Power of the Data Diode
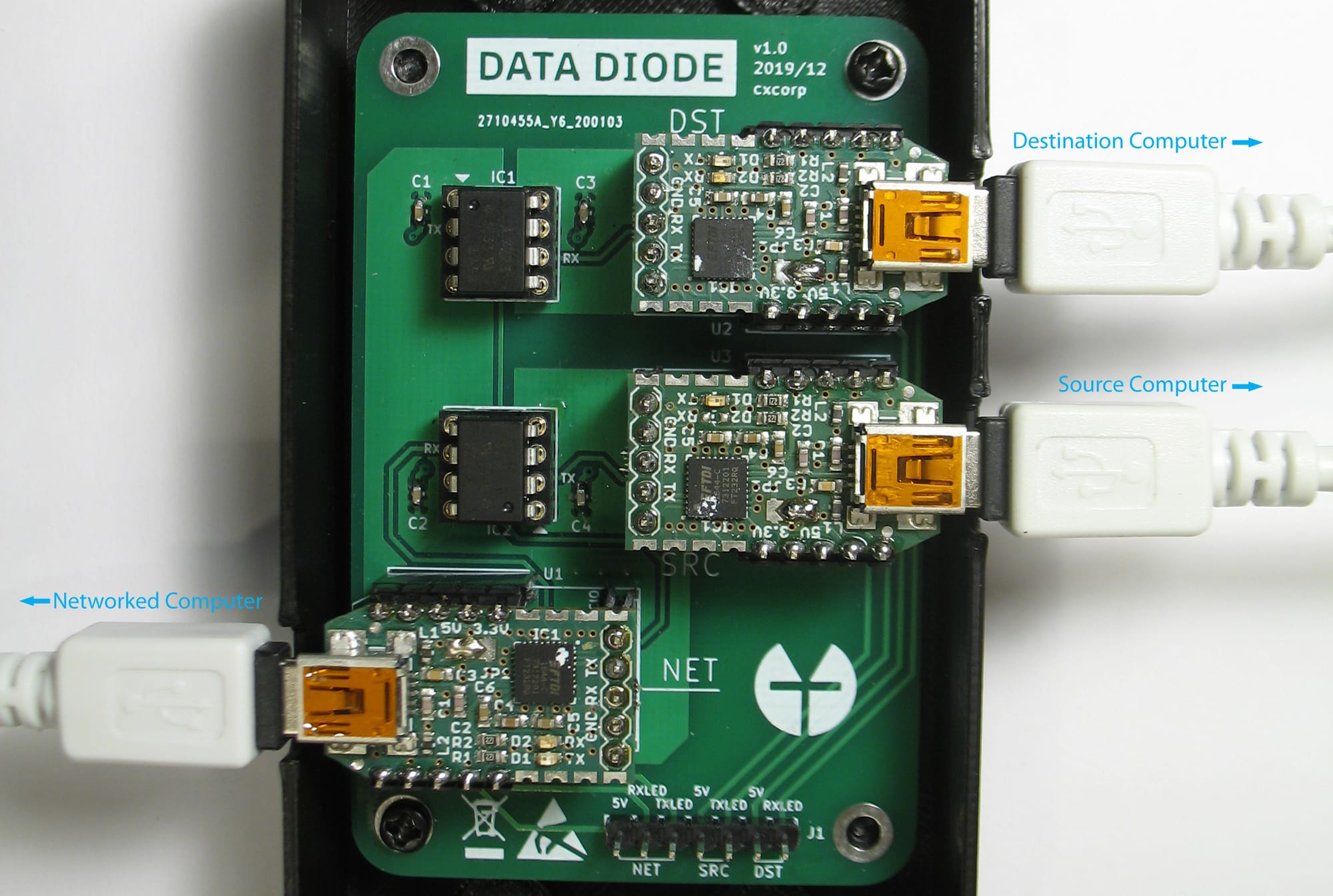
At the heart of TFC’s security measures lies the hardware data diode. This device ensures that data can only travel in one direction, effectively eliminating the possibility of reverse data flow. For legal communications, where even a single leak could have dire consequences, this feature is indispensable.
Consider the scenario where a lawyer is exchanging sensitive documents with a high-risk client. With a data diode in place, even if an attacker gains access to the networked computer, they cannot send any data back to the source or destination devices. This unidirectional flow guarantees that once the data is encrypted and sent, it remains out of reach from any malicious attempts to infiltrate or exfiltrate sensitive information. In essence, the data diode acts as a physical firewall—a barrier that no amount of sophisticated software-based attacks can penetrate.
Real-World Implications for Legal Practice

Beyond the technical marvels of TFC’s architecture lies its practical application in everyday legal practice. For lawyers, the stakes are incredibly high, and a single security breach can have far-reaching consequences. Let’s explore some scenarios where TFC could make all the difference.
Safeguarding Confidential Client Communications
Every lawyer knows that confidentiality is the cornerstone of the client–attorney relationship. When you’re dealing with high-risk clients—be it whistleblowers, victims of corporate malfeasance, or political dissidents—the potential fallout from a data breach is not just a professional embarrassment but could also endanger lives.
TFC’s robust encryption and hardware-based security measures ensure that every communication remains confidential. Even if a message is intercepted, the layered security means that the data is unreadable and the metadata is obscured. For a legal professional, this translates into a higher level of trust and assurance that sensitive client communications are protected against even the most persistent adversaries.
Mitigating Insider Threats and Unintended Data Leaks
Insider threats and inadvertent data leaks are two of the most challenging aspects of modern cybersecurity. Even with strict protocols, human error can sometimes lead to catastrophic breaches. TFC’s architecture, however, significantly reduces this risk. By isolating the critical functions of communication across multiple devices and enforcing unidirectional data flow, TFC ensures that even if one segment of the system is compromised—whether by malware or an insider—the sensitive data remains secure.
This level of protection is particularly relevant for law firms that handle highly sensitive cases. With TFC, even if a device used for routine communications becomes vulnerable, the encryption keys and the actual message content are kept isolated from any potential threat. This robust approach not only safeguards data but also upholds the stringent confidentiality requirements demanded by legal ethics and professional responsibility.
Enhancing Compliance and Client Confidence
Regulatory compliance and client trust are non-negotiable in the legal profession. With increasing pressure to protect client data against cyber threats, adopting a system like TFC can also help law firms meet stringent regulatory standards. The advanced security protocols embedded in TFC provide a compelling case for its use in environments where data protection is paramount.
Moreover, when clients know that their communications are being secured by a system that employs state-of-the-art cryptography, hardware isolation, and anonymous routing, their confidence in their legal representation is significantly bolstered. It sends a clear message that the law firm is committed to protecting client interests at every level, thus enhancing the firm’s reputation and credibility in an increasingly security-conscious world.
A Practical Example: Navigating a High-Stakes Case

Consider a hypothetical scenario: a lawyer is representing a client involved in a case against a powerful corporation accused of massive environmental violations. The corporation has deep pockets and a history of employing aggressive cyber tactics to intimidate adversaries. In this case, every email, document, and message exchanged between the lawyer and the client could be a potential target.
By employing TFC, the lawyer ensures that all communications are end-to-end encrypted, that the metadata is masked via onion routing, and that even if one device is compromised, the breach does not lead to a complete data exfiltration. The multi-device isolation ensures that the critical decryption keys remain locked away from any malicious actor. In such a high-stakes environment, TFC isn’t just an added layer of security—it becomes an essential component of the lawyer’s toolkit.
The Future of Secure Legal Communications
As technology continues to evolve, so too do the threats facing legal professionals. In this dynamic landscape, remaining ahead of adversaries requires not only a robust understanding of current security protocols but also a forward-thinking approach to future developments. TFC is more than a stopgap measure—it represents a transformative shift in secure communications that will shape the future of legal practice.
Embracing Innovation in Legal Tech
Legal technology is rapidly advancing, with secure communications now taking centre stage. The shift from traditional, single-layer encryption to multifaceted solutions like TFC underscores a critical realisation: the protection of client data must be holistic. As new forms of cyber attacks emerge, legal professionals are increasingly turning to innovative tools that not only encrypt data but also secure endpoints through hardware innovations such as data diodes.
Imagine a scenario where a lawyer, already burdened with the complexities of a high-profile case, need not worry about the potential fallout from a cybersecurity breach. With systems like TFC in place, the worry of sensitive data being intercepted is significantly diminished. This liberates legal practitioners to focus on the substantive aspects of their cases, confident in the knowledge that their communications are guarded by state-of-the-art technology.
Implementing TFC in Your Legal Practice
For law firms considering the integration of TFC, the transition may seem daunting. However, the benefits far outweigh the initial hurdles. Here are a few practical steps and considerations for implementing TFC into your practice:
- Assess Your Current Infrastructure: Begin by evaluating the existing communication channels within your firm. Identify any vulnerabilities, particularly at the endpoint level, where most traditional systems falter.
- Plan a Phased Integration: Implementing TFC doesn’t require a complete overhaul of your current system. A phased approach—starting with the most critical communications—can ensure a smooth transition.
- Train Your Team: Security is only as strong as its weakest link. Ensure that all team members are trained not only in the operational aspects of TFC but also in best practices for maintaining secure communications.
- Engage with IT Security Experts: Given the technical complexity of TFC’s multi-device architecture and hardware security measures, collaborating with cybersecurity professionals can provide invaluable guidance during the implementation process.
- Regularly Review and Update Security Protocols: Cyber threats evolve rapidly. Periodic reviews and updates of your security systems, including TFC’s configurations, will help maintain robust protection over time.
Overcoming Challenges and Building Trust
Transitioning to a system as robust as TFC may come with its set of challenges. For some, the multi-device approach might initially seem complex or cumbersome. However, the added layers of protection are precisely what high-risk legal cases demand. By embracing a more sophisticated communication model, law firms can significantly reduce the risks associated with traditional endpoint vulnerabilities.
Building trust—both within your team and with your clients—is another key benefit. When clients know that their legal representatives are utilising cutting-edge tools to safeguard their information, their confidence in your firm’s ability to protect their interests is naturally enhanced. This trust not only reinforces your professional reputation but also creates a competitive advantage in a field where confidentiality is paramount.
A Personal Reflection on Security in Law
I often reflect on the importance of secure communication in the legal profession. In today’s digital age, where the threat of cyber espionage is very real, every lawyer must be proactive in defending client confidentiality. The decision to integrate advanced tools like TFC isn’t merely about staying current—it’s about taking a stand against the pervasive risks that could undermine the very foundations of our justice system.
Imagine sitting in your office, sifting through sensitive case files, with the knowledge that every message you send is shielded by layers of robust encryption, unidirectional data flow, and the anonymity of onion routing. It’s a comforting thought that transforms the often daunting task of protecting client data into a well-orchestrated defence strategy. That is the promise of TFC—a promise that empowers legal professionals to navigate even the most perilous digital landscapes with confidence.
Securing the Future, One Message at a Time
In wrapping up our exploration of TFC and its profound implications for high-risk legal communications, one thing is abundantly clear: the future of legal practice lies in embracing advanced, multi-layered security systems. As cyber threats grow in sophistication, the need for a paradigm shift from traditional encryption methods to comprehensive security solutions becomes ever more pressing.
TFC stands at the forefront of this shift, offering a meticulously engineered approach that addresses every potential vulnerability—from the interception of encrypted data to the exfiltration of decryption keys. By integrating state-of-the-art cryptography, hardware-based endpoint security, and the anonymity of onion routing, TFC provides a robust and reliable communication framework that is tailor-made for the unique challenges faced by legal professionals.
For lawyers dealing with high-risk clients, TFC is not just a technical tool—it is a vital ally in the pursuit of justice. It reinforces the sanctity of the client–attorney relationship by ensuring that every confidential communication remains secure, even in the face of relentless cyber adversaries. In a world where the stakes are incredibly high, TFC offers a level of protection that transforms apprehension into assurance.
As you consider the future of your legal practice, think about the pivotal role that secure communications will play. The landscape of legal tech is evolving, and with it, the standards for client confidentiality are being redefined. Embracing innovative solutions like TFC can help ensure that your practice remains resilient, adaptive, and above all, secure.
TFC and the Future of Secure Legal Communications
In an era marked by rapid technological change and ever-escalating cyber threats, TFC emerges as a groundbreaking solution for legal professionals. Its multi-layered security model—combining state-of-the-art cryptography, hardware-enforced endpoint security, and onion routing—addresses the critical vulnerabilities of conventional communication systems. For lawyers handling high-risk cases, TFC is not merely an option; it is an essential tool in safeguarding client confidentiality and upholding the integrity of the legal profession.
As you move forward in your practice, consider how tools like TFC can be integrated into your security strategy. The future of legal communications depends on proactive measures that protect both your clients and your reputation. By investing in advanced security solutions today, you are not only securing your practice but also contributing to a safer, more resilient legal landscape for tomorrow.
For more details on TFC and to explore its advanced features, please visit the project’s GitHub repository at https://github.com/maqp/tfc.
